Aug 25., 2023 / Business
The Proxy-Puzzle: Demystifying Detection Strategies for a Safer Web Experience
The Proxy-Puzzle: Demystifying Detection Strategies for a Safer Web Experience
Introduction: In an increasingly interconnected world, the internet serves as a vital conduit for communication, commerce, and collaboration. However, this convenience comes with a caveat: the risk of malicious activities, including those facilitated by proxy servers. Proxy servers, once primarily used for privacy and anonymity, have become a double-edged sword, enabling both legitimate and harmful online activities. This article aims to unravel the intricacies of proxy VPN detection strategies, shedding light on how they contribute to a safer web experience for users and organizations.
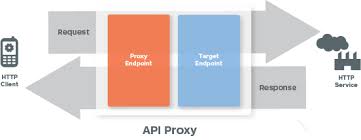
Understanding Proxies and Their Applications: Before delving into detection strategies, it’s crucial to understand the role of proxy servers. Proxies act as intermediaries between users and the internet, relaying requests and responses. While legitimate uses abound, such as load balancing and content caching, proxies can also facilitate cyberattacks, data breaches, and online fraud. This duality highlights the necessity of effective proxy detection mechanisms.
The Need for Proxy Detection: In an era where cyber threats are pervasive, organizations and individuals alike must safeguard their online platforms. Proxy detection plays a pivotal role in identifying the use of proxy servers to prevent unauthorized access, protect sensitive data, and maintain the integrity of digital spaces. By uncovering hidden IP addresses and unmasking the presence of proxies, detection strategies help mitigate risks and maintain a secure online environment.
Proxy Detection Strategies Demystified:
- IP Address Analysis: Proxy servers often manipulate IP addresses to conceal identities. Detection involves scrutinizing IP patterns, cross-referencing with blacklists, and analyzing geolocation data to uncover discrepancies that hint at proxy usage.
- Behavioral Analysis: This strategy involves monitoring user behavior, such as browsing patterns and interaction frequencies. Sudden deviations or anomalies can indicate the presence of a proxy, as human and proxy behaviors often differ.
- Anomaly Detection: Employing machine learning algorithms, anomaly detection identifies outliers in network traffic, flagging connections that exhibit unusual characteristics indicative of proxy use.
- Header Inspection: Proxies often leave distinctive headers in HTTP requests. By meticulously examining headers for signs of proxy involvement, detection mechanisms can expose attempts to mask true origins.
- CAPTCHA Challenges: Automated proxy access can be impeded through CAPTCHA challenges. Frequent CAPTCHA prompts can suggest proxy involvement, prompting further investigation.
The Balancing Act: False Positives vs. False Negatives: While robust proxy detection is essential, achieving a balance between minimizing false positives (legitimate users mistakenly flagged as proxies) and false negatives (proxy users escaping detection) is challenging. Fine-tuning detection strategies and leveraging multi-faceted approaches can strike this delicate equilibrium.
Future Directions and Innovations: The dynamic landscape of cybersecurity calls for continuous innovation in proxy detection. Advancements in AI and machine learning promise enhanced detection accuracy by learning from evolving proxy tactics. Additionally, collaborative threat intelligence sharing among organizations can fortify detection strategies and proactively combat emerging threats.
The “Proxy-Puzzle” is a complex enigma that demands careful unraveling. By understanding the nuances of proxy detection strategies, users and organizations can elevate their cybersecurity posture, ensuring a safer and more secure web experience. As technology evolves and threats mutate, the ongoing commitment to demystifying proxy detection remains paramount in the ever-changing landscape of digital security.












LEAVE A REPLY